Featured
Join Our Weekly Newsletter
Get articles and updates delivered straight to your inbox regularly.
No spam ever. Unsubscribe anytime easily.
Recent Posts
-
A Comprehensive Guide to Cybersecurity Attack Types and Defensive Strategies
Cybersecurity attack types represent the ever-evolving array of malicious actions…
-
Internet Traffic Routing Policies The Economic, Security, and Performance Mandates Governing BGP
Internet traffic routing policies are the fundamental rules and mechanisms…
-
Mastering Clinical Injection Techniques: A Comprehensive Guide to ID, SC, IM, and IV Routes
The practice of administering medications via injection is a cornerstone…
-
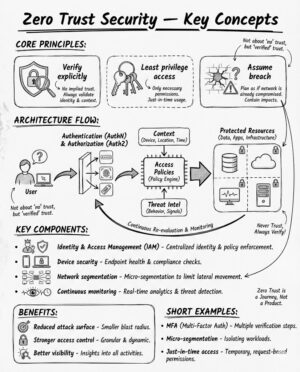
Zero Trust Security: Principles, Pillars, and Implementation for the Modern Enterprise
Zero Trust Security is a modern security framework requiring all…
-
Biological Wastewater Treatment: Principles, Processes, and Sustainability
Biological wastewater treatment (BWT) is a fundamental and critical process…
-
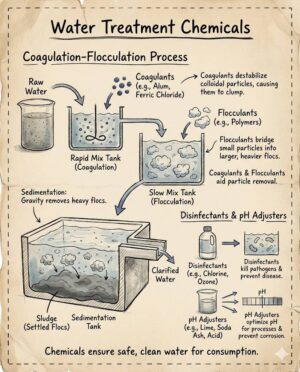
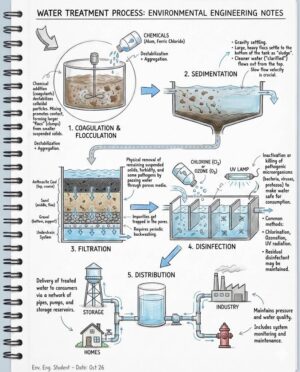
Mastering Chemical Formulation for Effective Water Purification
A comprehensive guide on water treatment chemicals formulation is an…
-
Chemical Formulation and Regulatory Compliance in Water Treatment
The imperative of the Water Treatment Process is foundational to…
-
Spermatogenesis vs. Oogenesis: The Two Divergent Paths of Gamete Formation
Spermatogenesis and oogenesis are the two pivotal processes collectively known…
-
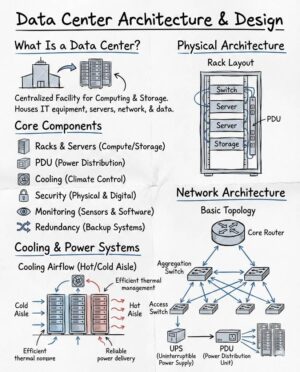
Data Center Architecture: Engineering for Resilience, Efficiency, and Scalability
The architecture and design of a modern data center represent…
-
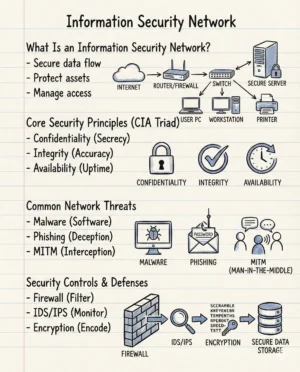
The Digital Citadel: Architecture and Evolution of the Modern Information Security Network
The foundation of any modern enterprise, regardless of its size…