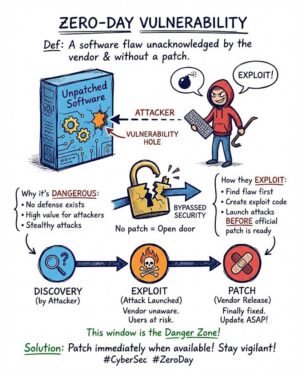
The concept of a zero-day vulnerability stands as one of the most critical and challenging security threats facing organizations and individual users today. A “zero-day” refers to a security flaw in software, hardware, or firmware that is recently discovered by attackers, often before the vendor or developer is even aware of its existence. The name derives from the fact that the developer has “zero days” to fix the flaw before it is actively exploited in the wild. This lack of vendor awareness and the subsequent absence of an available patch make zero-day vulnerabilities exceptionally dangerous, as conventional security defenses are typically designed to detect and block *known* threats. The speed at which attackers move to weaponize these flaws underscores a persistent reality for defenders: the exploitation window is extremely narrow, if it exists at all, before systems are compromised. The quiet, immediate nature of zero-day exploitation means these threats often operate silently, unlike larger, more disruptive volumetric attacks, making detection complex.
Understanding the terminology surrounding zero-day threats is crucial to grasping their mechanics. It is helpful to distinguish between the vulnerability, the exploit, and the attack. A zero-day vulnerability is the underlying security flaw itself—an error in the code or design that allows unauthorized access or unintended operations. Because vendors are unaware of the flaw, no security patch exists, making systems susceptible. A zero-day exploit, conversely, is the specialized code or method that hackers develop to specifically take advantage of that previously unidentified vulnerability. This exploit code functions as the mechanism of attack. Finally, a zero-day attack is the act of deploying the exploit to cause damage, compromise a system, or steal sensitive data. Once a vulnerability becomes publicly known and a patch is released by the vendor, the flaw is no longer technically a “zero-day” vulnerability, though the patched systems remain at risk until the mitigation is applied. The transition from discovery to widespread exploitation can happen incredibly quickly, necessitating an urgent response from both vendors and security professionals.
The severity of zero-day attacks stems directly from this gap in knowledge and remediation. Since security systems are fundamentally designed around known threats and existing patches, a zero-day exploit can often bypass even the most secure and up-to-date systems, including those used by banks or governments. When a vulnerability is eventually discovered, developers race to create and deploy a patch, but this process can take days, weeks, or sometimes months, leaving systems exposed in the interim. During this critical period, repeated exploitation of the zero-day can continue undetected for an extended duration. Because there is, by definition, no vendor-issued fix available to block the exploit, every system employing the vulnerable software or hardware is immediately at risk. This challenge highlights why zero-day exploits are considered more dangerous than those capitalizing on widely known vulnerabilities, even if historical data suggests most cyberattacks utilize already disclosed flaws. The risk is compounded by the fact that the security vulnerability often takes time to discover, even after the initial attack has occurred.
Researchers sometimes classify zero-day vulnerabilities based on their disclosure status. A vulnerability is considered “alive” if there is no public knowledge of its existence, granting the original discoverer immense power. Once the vulnerability has been disclosed publicly but remains unpatched, it may be classified as “dead.” In rare cases of unmaintained software, a vulnerability that has not been patched might be called “immortal.” The cost associated with acquiring or developing a zero-day exploit is significant, which historically made governments and state-backed groups the primary users. However, according to some research, any serious attacker can now access an affordable zero-day for almost any target, increasing the general risk level. Many targeted attacks, particularly those associated with advanced persistent threats (APTs), rely heavily on the initial access gained through zero-day vulnerabilities, confirming their place at the apex of cyber threats.
Zero-day vulnerabilities can be found across a vast array of technologies and attack vectors. Targets include fundamental systems and applications such as operating systems (like Windows or iOS), common web browsers (like Google Chrome and those using the Chromium engine), widely used office applications, open-source components, and even specialized hardware and firmware. With the expansion of interconnected devices, Internet of Things (IoT) devices are also increasingly vulnerable targets. Furthermore, recent trends indicate a significant expansion in the targeting of enterprise-specific technologies. This includes security and networking software and appliances, where a successful zero-day compromise can more effectively and efficiently lead to extensive system and network compromises, giving adversaries deep access to corporate infrastructure. In 2024, vulnerabilities in security and networking products accounted for over 60% of all zero-day exploitation of enterprise technologies, a stark indicator of this shifting focus. The increasing focus on these high-value enterprise products demands that a wider and more diverse set of vendors dedicate resources to proactive security measures.
Attacks utilizing zero-day vulnerabilities are broadly categorized into targeted and non-targeted campaigns. Targeted zero-day attacks are typically high-profile operations aimed at exceptionally valuable entities, such as large corporations, government agencies, or specific high-profile individuals. These attacks often rely on significant resources, as the cost of finding or purchasing zero-day vulnerabilities and subsequently writing the sophisticated attack software is substantial. Governments and state-backed groups engaging in cyber espionage are often cited as the primary users of the most expensive and potent zero-day exploits, accounting for over 50% of attributable vulnerabilities in 2024. Conversely, non-targeted zero-day attacks are waged against a broader user base of vulnerable systems, such as a popular operating system or a web browser. While not aimed at a specific individual, these mass campaigns aim to compromise as many users as possible, meaning even the average user’s personal data can be affected as collateral damage in a large-scale breach. Organizations subject to these attacks may observe tell-tale signs like unexpected traffic spikes or suspicious scanning activity originating from clients or services, though detection is notoriously difficult and remains an active area of research.
Historical examples underscore the real-world impact and varied targets of zero-day exploitation. In 2021, Google Chrome faced a series of zero-day threats, requiring the company to issue emergency updates. These vulnerabilities often stemmed from bugs within critical components, such as a flaw in the V8 JavaScript engine used in the web browser. The complexity of modern software means flaws can be deeply embedded. Even platforms lauded for their security, such as Apple’s iOS, have fallen victim. In 2020, iOS suffered from at least two sets of zero-day vulnerabilities, including a zero-day bug that allowed attackers to compromise iPhones remotely. More recently, in December 2025, Apple confirmed it had patched two WebKit zero-day vulnerabilities (CVE-2025-14174 and CVE-2025-43529) that were actively exploited in what the company described as “extremely sophisticated attacks against specific targeted individuals.” One of these, CVE-2025-14174, was also simultaneously patched by Google in Chrome, highlighting the collaborative and rapidly evolving threat landscape. The flaws were specifically a use-after-free issue and a memory corruption vulnerability, both caused by processing maliciously crafted web content. Such quiet, coordinated disclosures strongly imply the vendors recognized these bugs as extremely high-risk and likely already known to capable adversaries, necessitating immediate action to prevent wider abuse.
Other notable instances illustrate the devastating potential across different platforms. The Zerologon vulnerability, discovered in 2020, existed within Microsoft’s Netlogon Remote Protocol (MS-NRPC). It was a severe flaw that could allow an unauthenticated attacker with network access to a domain controller to completely compromise all Active Directory identity services. Another critical example is PrintNightmare (MSRPC Printer Spooler Relay vulnerability) found in the Windows Print Spooler service in 2021. Furthermore, there was a zero-day attack example involving hackers accessing a user’s PC remotely via a popular video conferencing platform if they were running an older version of Windows; if the target was an administrator, the hacker could achieve a complete takeover of the machine. Even attacks that seem mundane can have severe financial consequences, such as one zero-day exploit that compromised personal bank accounts after victims unwittingly opened a malicious Word document that requested external access from another program. Perhaps the most well-known historic case is the Stuxnet worm, a sophisticated cyber weapon that famously targeted industrial control systems in Iran, which utilized multiple zero-day vulnerabilities to successfully infiltrate and damage physical infrastructure. These cases reinforce the reality that zero-day exploitation is not theoretical; it is a continuously utilized and effective method of intrusion for adversaries.
The value of zero-day exploits has been amplified by the widespread adoption of encrypted communications. Since services like Apple, Google, Facebook, and Microsoft began encrypting messages and server data, the most feasible way for an attacker to gain access to a user’s data is by intercepting it at the source—the endpoint—before it is encrypted. This context has made zero-day exploits, particularly those targeting browsers and mobile devices, increasingly significant and valuable on the black market. Sellers and buyers who trade in zero-days maintain intense secrecy, often relying on non-disclosure agreements. This secrecy is necessary because if the vulnerability becomes public knowledge, it can be patched, and its monetary value subsequently crashes. Despite the lack of transparency in this clandestine market, the high demand for new, functional zero-days persists among various groups, including commercial surveillance vendors (CSVs) whose customers accounted for eight attributed zero-days in 2024, continuing their collective leading role alongside government-backed espionage actors.
Given that, by definition, no patch exists for a zero-day vulnerability when it is first exploited, effective defense requires a multi-layered, proactive strategy focused on reducing the attack surface and detecting anomalous behavior. One foundational measure is rigorous patch management. Although patches cannot prevent a zero-day attack if the exploit is created before the fix is deployed, systems must be updated immediately upon vendor release. Deploying software patches as quickly as possible after disclosure addresses known vulnerabilities and reduces the potential attack surface. However, patch management is complex, as applying patches can sometimes disrupt operations, necessitating a well-thought-out strategy that balances security requirements with operational stability. Furthermore, ensuring all systems—operating systems, applications, and drivers—are consistently up to date is crucial for general security hygiene, removing outdated features and fixing existing security holes that could otherwise be leveraged by subsequent stages of an attack.
Beyond standard patching, technical defenses focused on input validation are highly effective. Input validation involves the proper testing of any data supplied by an application or user to prevent improperly formed or malicious data from entering a system. This measure helps protect organizations in real-time by filtering out potentially harmful inputs that could target security vulnerabilities, even unknown ones. Deploying a web application firewall (WAF) on the network edge is one of the best preventative measures, as a WAF can review incoming traffic and filter out malicious inputs before they reach the vulnerable software. This capability enables organizations to respond dynamically to new, evolving threats that might represent zero-day attacks by preventing the attacker’s payload from executing on the target system. Input validation, therefore, adds a crucial layer of defense that operates continuously, regardless of current patch status.
Advanced security solutions must also be employed, moving beyond traditional antivirus software that relies solely on signature-based detection of known malware. Next-generation firewalls (NGFWs) are essential, as they incorporate deeper inspection capabilities and behavioral analysis techniques to identify suspicious software or traffic patterns that indicate an active threat. These modern techniques allow security infrastructure to block unknown zero-day malware by detecting deviations from normal behavior, even when the exploit signature is novel. Dynamic Application Security Testing (DAST) also serves as an invaluable preemptive measure. Unlike static methods that analyze code offline, DAST simulates external attacks on a live application, mirroring an attacker’s approach to uncover vulnerabilities—such as SQL injection and Cross-Site Scripting (XSS)—that are only visible during active operation. By continually testing applications from an outsider’s perspective, DAST helps in identifying and addressing security flaws before malicious actors can exploit them.
The cybersecurity industry also attempts to preempt the black market for vulnerabilities through programs like the Zero Day Initiative (ZDI) and bug bounty programs. The ZDI program rewards security researchers for privately disclosing vulnerabilities to vendors instead of selling them to hostile actors on the black market. Bug bounty programs serve a similar purpose, compensating individuals for ethically reporting vulnerabilities to the affected organizations. These initiatives aim to foster a community of vulnerability researchers who discover software problems before hackers do, creating a mechanism for responsible disclosure and remediation, thereby limiting the time a zero-day remains exploitable in the wild. Given the high value of zero-day vulnerabilities, this structured approach is crucial in redirecting the research effort toward defense rather than offense, though the value of a vulnerability that affects multiple vendors, products, and versions can complicate and extend the patch release timeline.
For end-users, several proactive habits significantly reduce the risk posed by zero-day threats. Since writing perfectly secure software is impossible, driving up the cost and complexity for an attacker to compromise systems is the goal. Conventional cybersecurity measures remain vital, including consistently enabling automatic software updates and practicing extreme skepticism regarding suspicious links or downloading attachments from unknown sources, as phishing emails often serve as the delivery mechanism for zero-day exploits. Furthermore, implementing strong access control is paramount. Using unique, complex passwords and enabling multi-factor authentication (MFA) everywhere possible adds an essential layer of protection. Even if an exploit compromises a system’s application layer, MFA can prevent the attacker from fully accessing an account. Finally, individuals should limit privileges by avoiding the use of an administrator account for everyday tasks and ensuring regular data backups are performed, which minimizes loss in the event of a successful breach, allowing systems to revert to a clean state if compromised.
The trends in zero-day exploitation continue to evolve, demanding that defenders adapt rapidly. Data from recent years shows a slow but steady growth in the overall rate of zero-day exploitation, with 75 zero-day vulnerabilities exploited in 2024 following a continuous pattern. Crucially, the target emphasis is changing. While end-user technologies (like browsers and mobile devices) remain popular targets due to the sheer volume of potential victims, there is a clear expansion toward enterprise-focused products, especially networking and security appliances. This tactical shift allows adversaries to achieve maximum network compromise efficiently. Conversely, vendor investments in robust exploit mitigations are starting to yield results; there has been a notable decrease in zero-day exploitation of some historically popular targets like mobile operating systems and browsers, suggesting that vendor efforts are having an impact on where threat actors are able to find success. However, sophisticated exploit chains composed of multiple zero-day vulnerabilities continue to be almost exclusively used to target mobile devices, maintaining that threat vector as extremely high-risk.
In conclusion, the zero-day vulnerability represents a fundamental challenge to digital security because it exploits the unknown. Effective mitigation requires organizations to shift from a reactive, patch-driven posture to a proactive, behavior-based detection strategy. By leveraging advanced security technologies like next-generation firewalls and DAST, enforcing strict access controls like MFA and least-privilege access, and ensuring employees are educated on safe online habits, the risk of successful zero-day attacks can be significantly reduced. As technology continues to advance and the threat landscape rapidly evolves, mastery of detection engineering and rapid response remains the critical backbone for protecting systems and ensuring operational resilience against these perpetually emerging threats. The comprehensive approach, involving continuous testing, instant protection delivery, and rapid patching, is the only way to minimize the time between a vulnerability being exploited and a final fix being deployed.
This ongoing evolution in the threat landscape demands constant vigilance and a synthesized understanding of current risks, ensuring that individuals and organizations are prepared not just for known threats, but for the vulnerabilities that have only just been, or have yet to be, discovered by those seeking exploitation. The necessity for the security industry to anticipate and block unknown threats in real-time makes the defense against zero-day attacks one of the most dynamic and critical fields in cybersecurity today.