In today’s hyperconnected environment, organizations and individuals rely heavily on computer networks to store, process, and transmit critical information. As networks expand and cyber threats grow more sophisticated, network security technology has become a foundational pillar of modern information security. Its primary goal is to protect network infrastructure, data, and services from unauthorized access, misuse, disruption, or destruction.
Understanding Network Security Technology
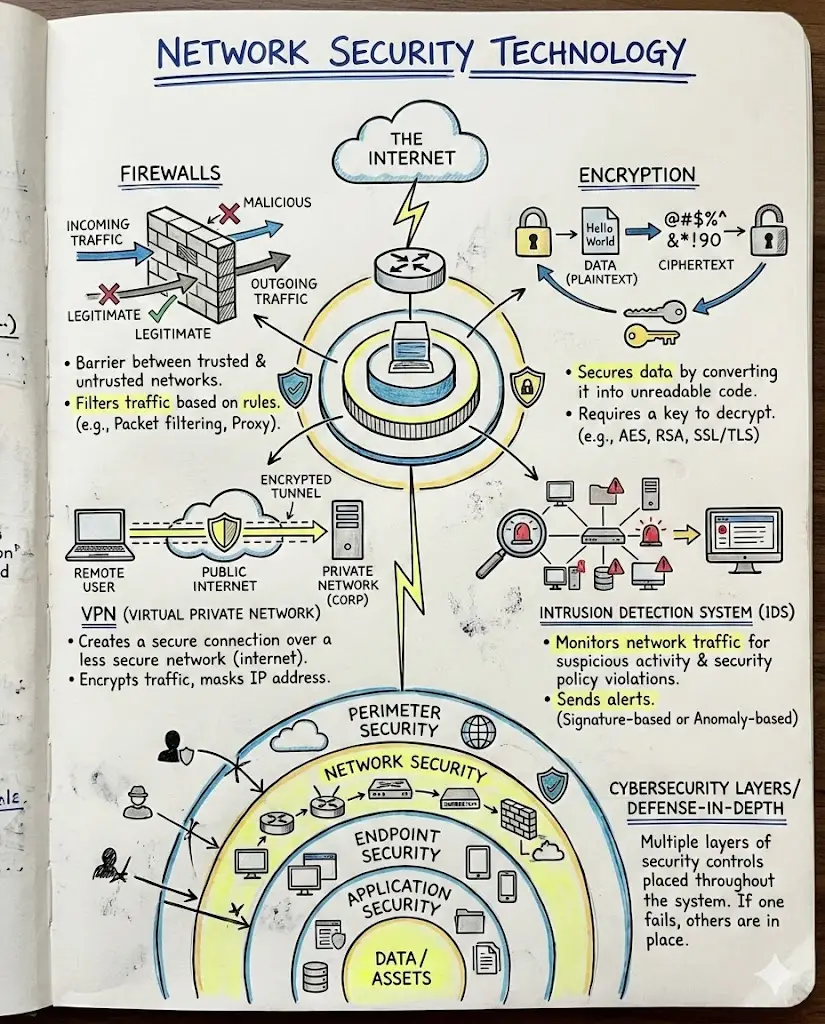
Network security technology refers to a collection of hardware, software, policies, and processes designed to defend networks from internal and external threats. Unlike single-point security solutions, network security is layered, meaning multiple technologies work together to provide comprehensive protection.
These technologies ensure:
-
Confidentiality – only authorized users can access data
-
Integrity – data is not altered during transmission
-
Availability – network resources remain accessible when needed
Key Components of Network Security Technology
1. Firewalls
Firewalls act as the first line of defense between trusted internal networks and untrusted external networks such as the internet. They monitor and filter incoming and outgoing traffic based on predefined security rules. Modern firewalls, often called next-generation firewalls (NGFWs), can also inspect application-level traffic and detect advanced threats.
2. Intrusion Detection and Prevention Systems (IDS/IPS)
-
Intrusion Detection Systems (IDS) monitor network traffic and alert administrators when suspicious activity is detected.
-
Intrusion Prevention Systems (IPS) go a step further by automatically blocking or mitigating detected threats.
These systems are essential for identifying malware, unauthorized access attempts, and unusual network behavior.
3. Virtual Private Networks (VPNs)
VPNs create secure, encrypted tunnels over public networks, allowing users to access private networks safely. They are widely used for:
-
Remote work
-
Secure communication between branch offices
-
Protecting data transmitted over public Wi-Fi
4. Encryption Technologies
Encryption protects data by converting it into unreadable formats that can only be decoded with the correct key. Network security relies on encryption protocols such as:
-
TLS/SSL for web traffic
-
IPsec for VPN connections
Encryption ensures that even if data is intercepted, it cannot be easily exploited.
5. Access Control and Authentication
Access control technologies determine who can access network resources and under what conditions. Common mechanisms include:
-
Usernames and passwords
-
Multi-factor authentication (MFA)
-
Role-based access control (RBAC)
Strong authentication significantly reduces the risk of unauthorized access.
6. Network Monitoring and Security Analytics
Continuous monitoring tools analyze network traffic in real time to detect anomalies and potential threats. By leveraging artificial intelligence (AI) and machine learning (ML), modern security analytics can identify patterns that indicate zero-day attacks or insider threats.
Emerging Trends in Network Security Technology
-
Zero Trust Architecture (ZTA): Assumes no user or device is trusted by default, even within the network perimeter. Every access request must be verified.
-
Cloud Network Security: As organizations migrate to the cloud, security technologies are evolving to protect hybrid and cloud-native environments.
-
Automation and AI-driven Security: Automated responses reduce reaction time to attacks and help manage complex networks efficiently.
Challenges in Network Security
Despite advancements, network security faces several challenges:
-
Increasing volume and sophistication of cyberattacks
-
Shortage of skilled cybersecurity professionals
-
Complexity of managing security across hybrid and remote environments
Addressing these challenges requires not only technology but also strong governance, user awareness, and continuous improvement.
Conclusion
Network security technology is essential for protecting digital assets in an increasingly connected world. By combining firewalls, intrusion prevention systems, encryption, access controls, and advanced analytics, organizations can build resilient defenses against evolving cyber threats. As technology continues to advance, network security will remain a dynamic field, adapting to new risks and playing a critical role in ensuring trust, privacy, and stability in the digital ecosystem.