In an era where computational workloads are the lifeblood of business operations, data center security has evolved from a technical necessity into a strategic imperative. A comprehensive security plan must shield servers, networks, and power systems from an increasingly sophisticated landscape of internal and external threats.
Why Security is Critical
Whether utilized for primary storage, disaster recovery, or hosting business-critical applications, data centers are high-value targets. Robust security ensures:
- Business Continuity: Minimizing downtime during attacks or natural disasters.
- Data Integrity: Protecting sensitive information from unauthorized modification.
- User Confidence: Allowing stakeholders to focus on growth without fearing digital asset loss.
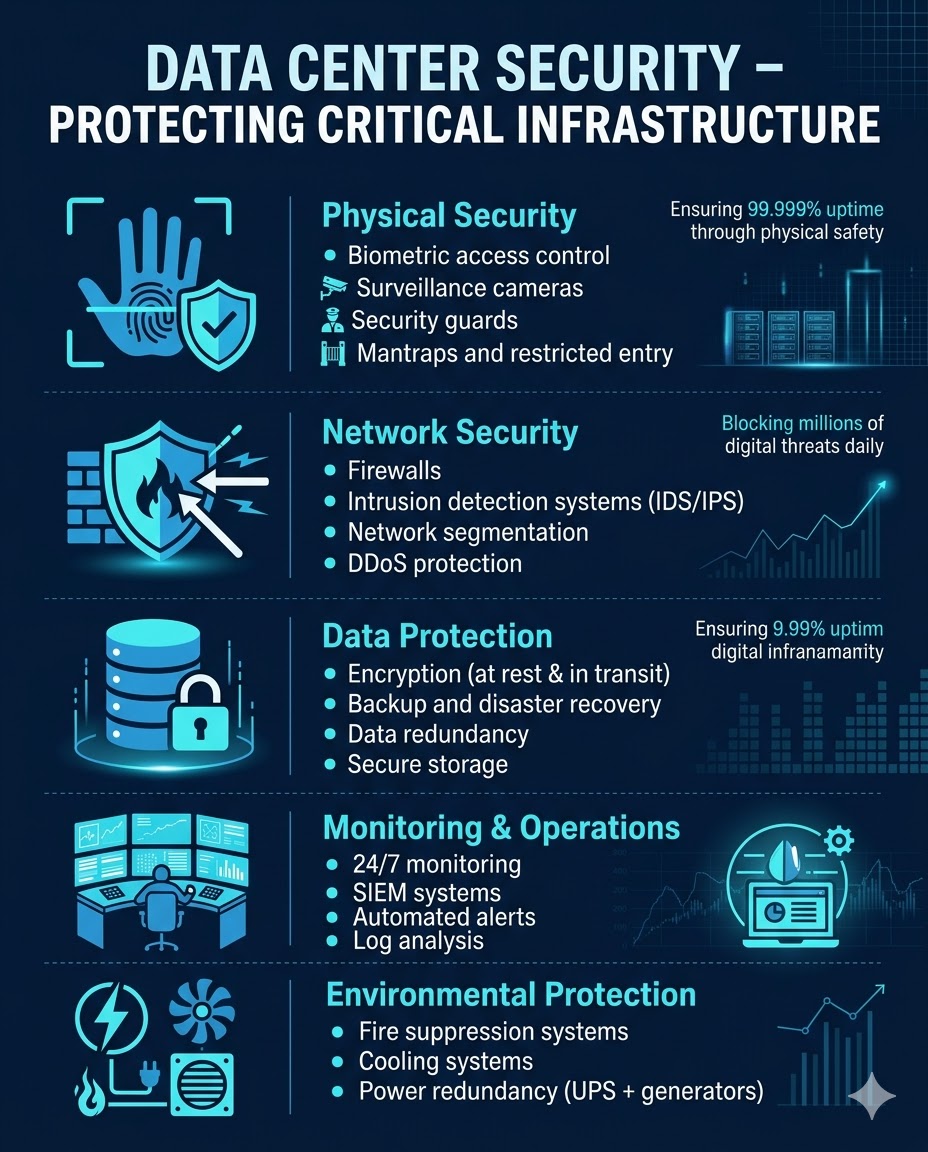
1. Physical Security: The First Line of Defense
Securing a data center begins with the “where” and “how” of its construction.
- Strategic Location: Avoid high-risk areas such as earthquake fault lines, flood plains, flight paths, and regions prone to wildfires or hurricanes.
- Structural Integrity: Utilizing reinforced materials, like concrete walls at least one foot thick, can protect equipment from explosions or extreme weather.
- Access Control: Physical entry should be guarded by multiple layers of verification, including:
- Government-issued ID checks and visitor badges.
- Biometrics: Fingerprint identification, retina scans, or facial recognition.
- Electronic badge key cards and physical keys for sensitive equipment zones.
- Surveillance: Continuous monitoring acts as both a deterrent and a forensic tool to track unauthorized activity.
2. Virtual and Software Security
As data centers leverage virtualization and public cloud services like AWS, the digital attack surface expands. Essential virtual safeguards include:
- Network Protections: Deploying network security tools like firewalls and Next-Generation Firewalls (NGFWs) to control traffic and prevent malware.
- Intrusion Systems: Using detection and prevention systems to identify suspicious patterns in real-time.
- Strong Authentication: Implementing Two-Factor Authentication (2FA) or Multi-Factor Authentication (MFA) to ensure that stolen passwords alone aren’t enough to grant access.
3. Resiliency through Redundancy
Redundancy is the practice of having “backup” components ready to take over if a primary system fails. This is vital for both performance and security:
- Infrastructure: Redundant power supplies, cooling systems, and internet service providers (ISPs) maintain uptime.
- Security Insight: Running dual firewalls (e.g., at the edge and in front of the server) allows administrators to inspect traffic that bypasses the first layer, providing insight into internal vulnerabilities.
Addressing Vulnerabilities
Human error remains a significant risk. Attackers often use social engineering or ransomware to bypass technical controls. To mitigate these risks, organizations must:
- Educate Personnel: Train users on credential management and how to spot phishing attempts.
- Automate Updates: Use threat intelligence to automatically update software against the latest known exploits.
- Enforce Password Hygiene: Discourage password recycling, which allows hackers to move laterally across different systems.
Note: A secure data center is not a static achievement but a continuous process of updating technology and educating the workforce to stay ahead of evolving threats.